Use case
A new activity needs a risk assessment. Who's doing it and how?
Create a structured risk assessment using templates, score each risk, document mitigations, assign follow-up tasks. Send it to everyone involved; they acknowledge before the activity starts. Six months later, acknowledgements stay timestamped on one record.
Right now, risk assessments are created once, filed somewhere, and rarely revisited.
A school trip is being planned. Someone creates a risk assessment in Word, emails it to the trip leaders, and it gets saved in a folder. Whether everyone actually read it, and whether the version they read is the current one, is anyone's guess.
Risk assessments exist, but they sit in isolation: away from the people they cover, the activities they describe, and any proof that the right people read and signed them.
See it in action
With modules connected, the workflow looks like this.
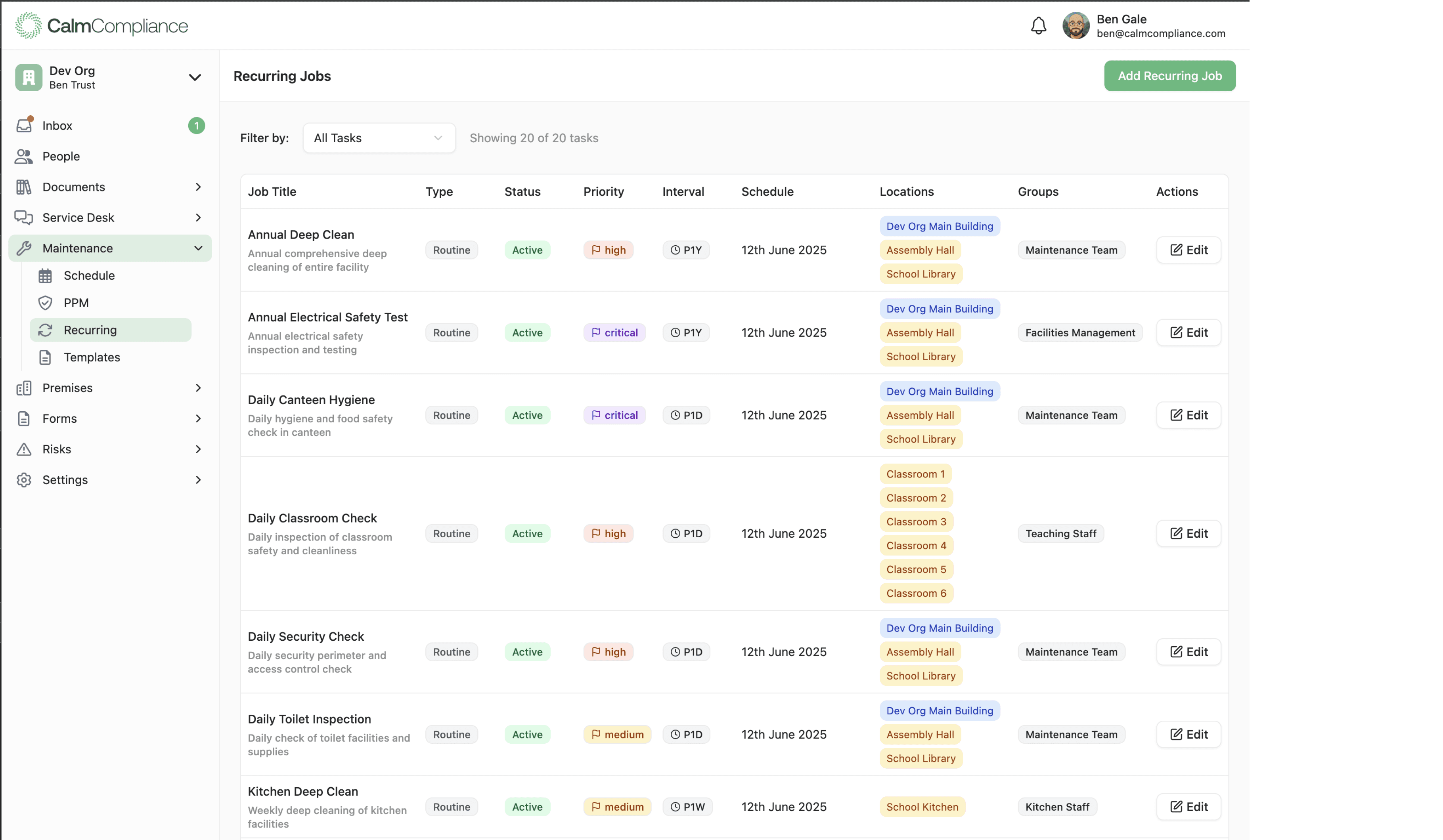
Built from a structured template
Start from a template. Score each risk. Document your controls.
Create a new risk assessment for the trip, activity, or premises change, from scratch or from a reusable template. Add risk items using the structured format: describe the hazard, score severity and likelihood, record existing controls, and document mitigations. Assign follow-up tasks to specific people, linked directly to the risk item they're addressing.
- Start from a template, not a blank page.
- Reusable templates and modular risk sets mean common assessment types are ready to go. Adapt for this activity rather than starting from scratch.
- Severity × likelihood scoring built in.
- Score each risk and the matrix calculates overall risk level automatically, flagging high-priority items.
- Mitigations and tasks linked to each risk.
- Record control measures and assign follow-up tasks directly against the risk item they address.

Distributed and acknowledged
Everyone who needs to sign it, signs it. With a timestamp.
The completed risk assessment is distributed to all staff involved. They must acknowledge it before the activity starts. Each acknowledgement is timestamped and linked to their record. You can see at a glance who has and hasn't signed, and anyone who hasn't receives a reminder automatically.
- Distributed directly from the risk assessment.
- Select who needs to see it. They receive it on their device and must acknowledge before the activity.
- Every acknowledgement timestamped.
- Signed, dated, linked to the person's record. Provable evidence that it was read.
- Outstanding acknowledgements chased automatically.
- If someone hasn't signed, a reminder goes out. You see who's still outstanding at a glance.

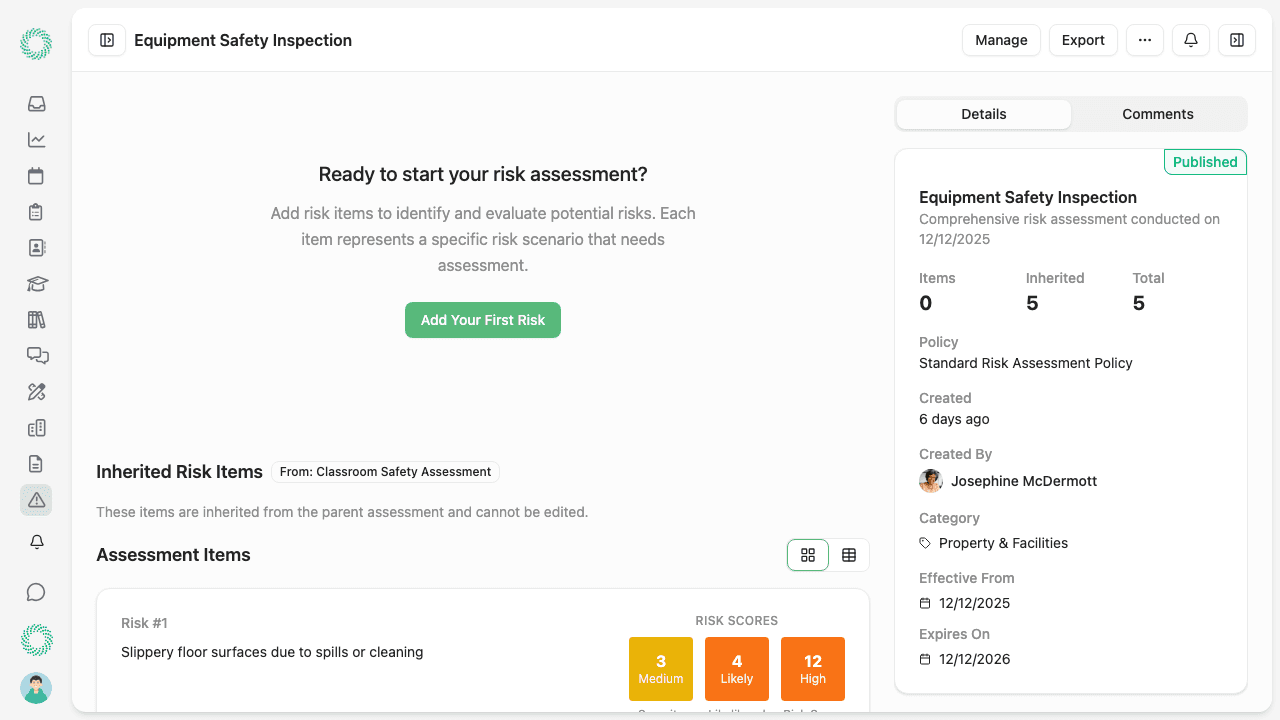
Six months later
Someone asks who signed off what. You open one record.
A parent raises a concern. A regulator asks for evidence. An insurer wants to see the risk management process. You open the risk assessment record. There's the assessment as it was distributed, with acknowledgements timestamped, linked to each staff member's record, and the follow-up task that was assigned and completed.
- Version history maintained automatically.
- Every change tracked. The distributed version is preserved exactly as it was signed.
- Acknowledgements linked to staff records.
- Not just a name: linked to the person's role and their record in the system.
- Complete audit trail, provable on demand.
- From creation to acknowledgement to follow-up, everything in one record.

What you're replacing
This workflow works the same way everywhere.
The details change depending on your world.
Schools & Children's Services
Trip risk assessments, event planning, activity hazards: created from templates, distributed to relevant staff, acknowledged before the activity starts. Evidence built in for any inspector or regulator.
Care Homes
Resident care plan reviews, environmental risk assessments, new admission risk profiles: created, distributed, and acknowledged. Evidence that risk is actively managed, ready for any inspection.
Facilities Management
Contractor risk assessments, building works, change management: reviewed, signed off, and linked to the project record. Evidence for clients and compliance auditors.
Manufacturing & Warehousing
COSHH assessments, manual handling reviews, new process risk assessments: distributed to affected teams, acknowledgements tracked. H&S evidence always provable.
Leisure & Hospitality
Event risk assessments, seasonal activity risks, public access changes: all managed in one system. Evidence ready for the local authority, insurer, or regulator.
Related use cases
An inspector is coming
Risk assessments are part of the inspection evidence picture. See how they connect to policies, training, and maintenance in one audit-ready view.
See use case →A new starter joins
New starters need to acknowledge relevant risk assessments on joining. See how the onboarding workflow connects to risk management.
See use case →Something goes wrong
When an incident occurs, the risk assessment is part of the investigation record. See how incidents and risk connect in the same system.
See use case →
See it for yourself.
Book a demo and we'll walk through how risk assessment creation, distribution, and acknowledgement works using a scenario relevant to your organisation.